sungo.io
About - RSS - CodePosts
- - I Use This: Leg disability edition
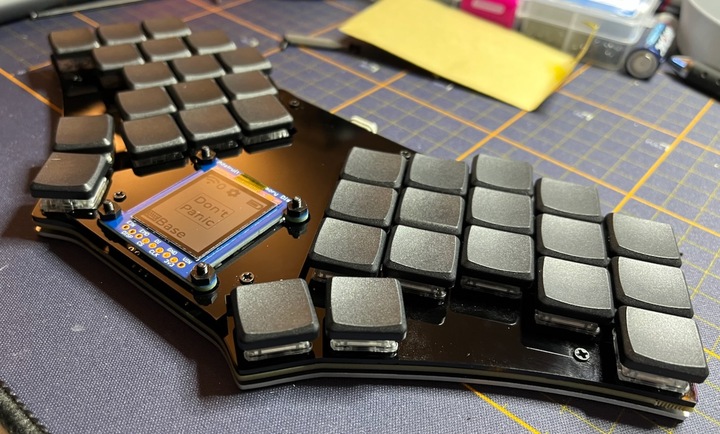
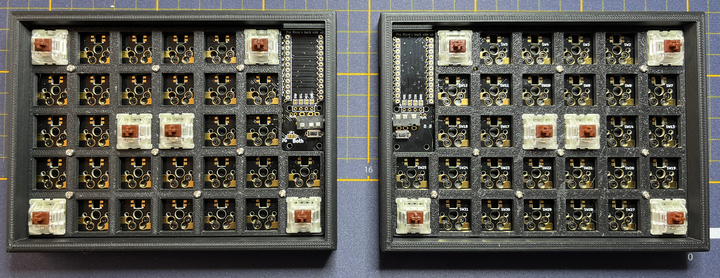
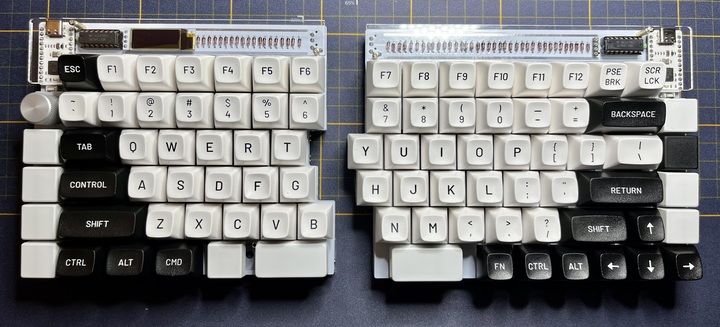
- - Keyboards
- - Emacs + gopls = 100% cpu
- - Ramblings
- - Prototyping a trackball
- - 2021: The Year Of Keyboards
- - Printing PC on a Prusa
- - My 3D Models
- - GPG: Strong Keys and Rotation (reissue)
- - 3D Printer Roundup: MatterHackers Pulse XE
Keyboard Builds
-- All Keyboards | RSS Feed--
Models
- - Corne MCU Cover
- - Nespresso Vertuo Dispenser
- - Fume Extractor
- - Barrel Jack Junction v2
- - Duet Smart Effector Fan Support
- - Walmart Lamp Shade
- - TLM Wire Guide
- - TLM Fan Deflector Remix
- - TLM Duet Front Plate
- - Adafruit Environmental Sensor
-- All Models | RSS Feed--